4 min read
Perimeter Fences: From Basic Chain Link to High-Security Solutions
![]() Theseus Team
:
Jun 17, 2024 8:30:00 AM
Theseus Team
:
Jun 17, 2024 8:30:00 AM

Perimeter fences are a fundamental aspect of physical security, serving as the first line of defense for a wide range of facilities, from residential properties to high-security installations such as nuclear facilities. And while providing an appropriate level of security is paramount, considering aesthetics is also important.
Below, we explore the various perimeter fences, starting from the lowest security and progressing to the highest security applications commonly used in the United States. We also discuss common intrusion detection systems integrated with these fences.
Chain Link Fences
 Basic Chain Link Fences
Basic Chain Link Fences
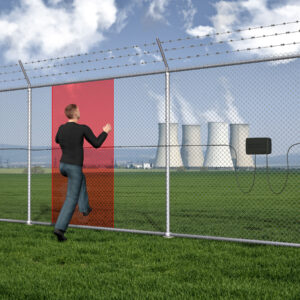
Chain link fences are among the most common and cost-effective perimeter fencing solutions. They are widely used in residential areas, schools, and recreational facilities. These fences typically consist of a woven steel wire mesh mounted on steel posts, forming a diamond pattern. While they are effective at delineating boundaries and deterring casual trespassers, their security level is relatively low, especially when not installed around the entire area as we see in this article's image.
Example: School Playground Fence
A school playground might use a 4 to 6-foot high chain link fence to keep children within the designated play area. These fences are usually not fortified and may not surround all sides of the area, relying on natural barriers or other structures to complete the enclosure.
Enhanced Chain Link Fences
For slightly higher security needs, enhanced chain link fences can be installed. These may include additional features such as barbed wire or razor wire on top, increased height (up to 10 feet or more), and thicker gauge wire.
Example: Commercial Property Fence
A commercial property, such as a warehouse or distribution center, might employ an 8-foot high chain link fence with three strands of barbed wire at the top. This setup provides a higher level of deterrence against unauthorized access.
 Welded Wire Mesh Fences
Welded Wire Mesh Fences
Welded wire mesh fences offer improved security over basic chain link fences. The wire mesh is welded at each intersection, creating a more rigid and tamper-resistant barrier. These fences are commonly used in industrial settings, parks, and utility sites.
Example: Utility Substation Fence
A utility substation might use a welded wire mesh fence with a height of 8 to 10 feet, combined with anti-climb features and possibly an anti-dig skirt to prevent intruders from digging underneath the fence.
 Palisade Fences
Palisade Fences
Palisade fences are known for their robust construction and intimidating appearance. Made from steel or iron, they consist of vertical pales secured to horizontal rails. The tops of the pales are often pointed or have other anti-climb features, making them difficult to scale.
Example: Industrial Facility Fence
An industrial facility, such as a manufacturing plant, might use a palisade fence with a height of 10 to 12 feet, with pointed pales and additional security features like CCTV cameras and motion sensors.
 High-Security Fences
High-Security Fences
High-security fences are designed for critical infrastructure and high-risk sites. These fences incorporate advanced materials and technologies to provide maximum security. They often include multiple layers of protection, electronic surveillance, and are designed to resist cutting, climbing, and breaching.
Anti-Ram Fences
Anti-ram fences are designed to prevent vehicle breaches. They are constructed to withstand high-impact collisions and are often used to protect sensitive installations.
Example: Military Base Fence
A military base might employ anti-ram fencing with reinforced steel and concrete barriers, capable of stopping a vehicle traveling at high speed. These fences are integrated with surveillance systems and access control points.
 Highest Security Fences: Nuclear Facilities
Highest Security Fences: Nuclear Facilities
Nuclear facilities require the highest level of security to protect against potential threats. The fences used in these settings are part of a comprehensive security system that includes physical barriers, electronic detection, and response protocols.
Example: Nuclear Power Plant Fence
A nuclear power plant would use multiple layers of high-security fencing, starting with an outer perimeter fence made of anti-climb, welded wire mesh with barbed wire. Inside, there might be a final layer of a reinforced concrete barrier. The entire perimeter would be monitored by advanced surveillance systems, including thermal cameras, motion sensors, and pressure-sensitive ground sensors. Access points would be strictly controlled with biometric authentication and armed security personnel.
Common Intrusion Detection Systems
To enhance the security provided by perimeter fences, various intrusion detection systems can be integrated. These systems are designed to detect and alert security personnel to any attempts to breach the fence. Commonly used systems include:
 Coaxial Cable Systems
Coaxial Cable Systems
photo courtesy of Southwest Microwave
Coaxial cable intrusion detection systems use sensitive coaxial cables attached to the fence. These cables detect vibrations and disturbances caused by climbing, cutting, or tampering with the fence. When an intrusion is detected, the system triggers an alarm and can provide precise location information.
Example: Coaxial Cable System on a Commercial Property Fence
A facility might enhance its chain link fence with a coaxial cable detection system, ensuring any attempt to climb or cut the fence is immediately detected and alerted to security personnel.
Fiber Optic Cable Systems
 photo courtesy of Senstar
photo courtesy of Senstar
Fiber optic cable systems are highly sensitive and capable of detecting minute vibrations along the fence line. These systems use fiber optic cables to detect disturbances and provide real-time alerts to a central monitoring system. They are highly effective in various environmental conditions and can cover long distances.
Example: Fiber Optic System on a Utility Substation Fence
A utility substation might integrate a fiber optic intrusion detection system with its welded wire mesh fence, ensuring any intrusion attempts are detected and the exact location is reported for a swift response.
Perimeter fences are a crucial component of physical security, with applications ranging from simple boundary delineation to the highest security requirements for critical infrastructure. By understanding the various types of fences, their appropriate use cases, and the integration of advanced intrusion detection systems, security professionals can design and implement effective perimeter security solutions tailored to specific needs and threats.
Creating an effective perimeter protection design for your facility is paramount. No need to spend more than you need to and you must also be careful to properly secure sensitive facilities. The Theseus Professional Services team provides physical security consulting and engineering services for data centers, hospitals, campuses, government agencies, and more. Contact us today to discuss your security challenges.
Learn more about perimeter protection strategies here



